- quickq加速器官网-Quickq可以登录多个设备-袋鼠vp加速器
- hammer加速器testflight-testflight开发人员将您从测试程序中删除是什么意思?-佛跳墙vnp
- 雪狼加速器-冒险岛机械师升级路线-袋鼠vp加速器
- xf30旋风加速器-我可以将抖音与旋风加速器一起使用吗?-佛跳墙vnp
- 坚果加速器app苹果版-坚果APP可以在iPhone上使用吗?-佛跳墙vnp
- 永久免费的连外网的软件-如何在外网(不在同一个局域网内)实现资源共享?,你要什么软件??-袋鼠vp加速器
- 永久免费外网加速器推荐-有什么好的免费加速器-佛跳墙vnp
- 云帆一小时-易连有梦戴小燕的演员是谁,请给我答案-袋鼠vp加速器
- 天行加速器官网-天行超级加速器显示正在请求-佛跳墙vnp
- 黑洞加速器电脑版下载-loco加速器电脑版怎么下载-袋鼠vp加速器
- 飞机加速app-为什么飞机加速器连不上?-袋鼠vp加速器
- nuts加速器-NutsAccelerator的官方网站是什么?找了好久都找不到!-袋鼠vp加速器
- 永久免费外网加速器-我在哪里可以找到免费的在线游戏加速器?-佛跳墙vnp
- 免费加速器梯子-我应该使用什么加速器来玩PUBG。-佛跳墙vnp
- 多快加快器-十大加速器排行榜,哪个游戏加速器比较好?-佛跳墙vnp
- 起飞加速vpv-VPN加速器原理-袋鼠vp加速器
- 阿特加速器下载-如何使用加速器?-袋鼠vp加速器
- 老王加速最新版v2.2.21下载-在哪里下载法老王vpn-袋鼠vp加速器
- 狗急加速器官网-狗从墙上跳下来-袋鼠vp加速器
- 鹰眼加速器破解版-迅游最新破解版-佛跳墙vnp
- 极光网络加速器-在哪里删除AuroraMasterAccelerator-袋鼠vp加速器
- 佛跳墙官方下载2024-电视剧佛跳墙下载地址-佛跳墙vnp
- 永久免费加速器-全球加速器永久免费送货时间-袋鼠vp加速器
- 如梭加速-班车呢?安全吗?-袋鼠vp加速器
- 免费爬梯子加速器-有哪些好的游戏加速器?-佛跳墙vnp
- 边缘加速器ios-IOS有什么加速器?-袋鼠vp加速器
- 海鸥npv加速器官网-优途vp加速器-袋鼠vp加速器
- 神灯vp加速器外网-盒子和神灯哪个更好?哪个加速器更好用?-佛跳墙vnp
- 考拉加速器官网下载-下载加速器在哪里下载?-佛跳墙vnp
- 梯孑加速器-雷神加速器是梯子吗?-佛跳墙vnp
- 蜜蜂加速器ios下载-蜜蜂加速器过期了-袋鼠vp加速器
- 云末加速器官网下载-美服冒险岛官网?-佛跳墙vnp
- 蜂鸟加速器官网-电脑上总有蜂鸟软件卸载不掉怎么办?-袋鼠vp加速器
- 佛墙官方网-佛跳墙有苹果版吗?-袋鼠vp加速器
- quickq电脑版下载-怎么下载quickq-袋鼠vp加速器
- 国内免费梯子加速器-中国最好的网络游戏加速器是什么?-佛跳墙vnp
- pixiv加速器永久免费-我可以在pixiv手机上输入哪些加速器?-袋鼠vp加速器
- 坚果加速器官网-坚果加速器一直加载?-袋鼠vp加速器
- quickq充值官网-怎么下载quickq-袋鼠vp加速器
- 雷霆加速器外网下载-是不是有朋友要求下载迅雷加速器,然后做任务赚钱?-佛跳墙vnp
- 小火箭免费节点下载-是否有可能拥有一个小型火箭服务器节点?-佛跳墙vnp
- 神灯加速-使用神灯加速器安全吗?-佛跳墙vnp
- 云梯加速器下载-垂直梯加速器的使用方法-佛跳墙vnp
- 黑洞加速器ins-黑洞加速器有病毒吗?-袋鼠vp加速器
- 飞鸟加速器永久免费版-四个永远免费的加速器-袋鼠vp加速器
- 云帆免费一小时-云帆小说阅读器软件介绍-佛跳墙vnp
- 香蕉vp加速器安卓-如何使用加速器-佛跳墙vnp
- lantern官方网站-灯笼(蓝光)mac版安装后打不开怎么办?-佛跳墙vnp
- 梯子加速免费-梯形加速器是什么意思?-佛跳墙vnp
- fotiaoqiang-什么是佛跳墙?-袋鼠vp加速器
- 哔咔哔咔加速器-如何解决一直在加载的哔声解决方案-佛跳墙vnp
- 免费加速器ios下载-怎么下载quickq-佛跳墙vnp
- 黑洞加速噐官网下载-玩游戏不卡顿的加速器有哪些?-佛跳墙vnp
- 极云加速器app-手机转电脑软件-佛跳墙vnp
- 银河加速npv官网下载-有哪些免费的加速器?-佛跳墙vnp
- 袋鼠加速器ios-袋鼠加速器怎么用?-佛跳墙vnp
- 狗急加速器下载-狗加速器有什么用-佛跳墙vnp
- 天行npv官网-谁有蓝光,天际线软件下载,急O(∩_∩)O谢谢-佛跳墙vnp
- 云梯加速器好用吗-加速器是静态的还是动态的?-袋鼠vp加速器
- 神灯app加速器-神灯加速器是国产的还是国外的?-佛跳墙vnp
- 边缘加速-附在手机边缘的一键加速球不见了,怎么取出来?好像是在清理球,在清理背景-袋鼠vp加速器
- 山羊vp加速器-如何在模拟山羊丰收日解锁所有绵羊-袋鼠vp加速器
- 可以加速哔咔的加速器-你能看视频吗?-佛跳墙vnp
- 蘑菇加速官网-蘑菇加速器成员是否受到限制?-佛跳墙vnp
- 油管加速器永久免费版-找一个永久免费的网游加速器,在家玩游戏延迟太高,一定要稳定!-佛跳墙vnp
- 免费国外网站加速安卓-有哪些免费加速器可以加速国外服务器手游?-佛跳墙vnp
- 加速器梯子推荐免费-哪种蒸汽加速器更好?-佛跳墙vnp
- 加速器外网免费下载-什么加速器可以加快大文件的下载速度?-袋鼠vp加速器
- 旋风vp加速器官网下载-我在哪里可以下载iPhone版CycloneAccelerator?-袋鼠vp加速器
- 西游vp加速器-迅游加速器好用吗?-佛跳墙vnp
- 彗星加速器app下载-什么是彗星dns优化器以及如何使用它?效果如何?-袋鼠vp加速器
- 云梯加速器官网-天梯软件下载,高分奖励-袋鼠vp加速器
- 狗急vp-热闹的自我治疗VPJO-佛跳墙vnp
- 梯子加速器app永久免费-在Instagram上使用哪个加速器(免费)-袋鼠vp加速器
- 全球海外加速器-加速器只在海外活动是什么意思-佛跳墙vnp
- 无极加速器免费-有哪些免费的加速器?-袋鼠vp加速器
- quickqios下载-quickq苹果版不能用-袋鼠vp加速器
- 外网vp加速器官方下载-在Twitch手机上使用什么加速器-袋鼠vp加速器
- seagullvp官网-基金公司VP是什么职位?-佛跳墙vnp
- 如梭加速器vp-玩游戏不卡顿的加速器有哪些?-袋鼠vp加速器
- 免费梯子外网加速器2024-腾讯网游加速器很多游戏都不能加速。你在骗钱吗?-袋鼠vp加速器
- 蚂蚁海外加速器二维码-如何在iPhone上使用Ant加速器?-佛跳墙vnp
- 极光加速器-在哪里删除AuroraMasterAccelerator-袋鼠vp加速器
- 加速器蚂蚁-蚂蚁加速器靠谱吗?-佛跳墙vnp
- 云墙加速器官网-请问可以用哪个加速器玩slither.io的战斗?-佛跳墙vnp
- 老王vp下载地址官网-哪个通用相机驱动程序最好用?下载地址是什么?-佛跳墙vnp
- 描王加速器-如何使用前进加速器-袋鼠vp加速器
- 小火箭vp加速器-小型火箭加速器是垃圾-佛跳墙vnp
- 快喵加速器ios下载官网-企鹅加速器-袋鼠vp加速器
- lantern官方网站-如何破解蓝光灯笼流量无限使用?-佛跳墙vnp
- 免费网页加速器-有没有网页游戏加速器-袋鼠vp加速器
- vpn神灯-关于服务器租用的问题神灯网络科技的服务器怎么样?-袋鼠vp加速器
- 捶子加速器-坚果加速器打不开-佛跳墙vnp
- 袋鼠加速器下载官网-我可以在不使用手机账单的情况下使用袋鼠加速器的网络吗?-袋鼠vp加速器
- 免费外网加速软件-哪个加速器最适合手机-佛跳墙vnp
- 极云加速器geeyun-极云加速器收费吗?-袋鼠vp加速器
- p站加速器下载-ioswatchP站用的是什么加速器?-佛跳墙vnp
- ssr加速器安卓下载的-ssr加速器可以加速roblox吗?-佛跳墙vnp
- 加速器安卓永久免费-哪些安卓手游加速器好用?-佛跳墙vnp
- 佛跳墙2024-陈赫有多少次过自己向往的生活?-佛跳墙vnp
极光网络加速-使用极光加速器违法吗?-佛跳墙vnp

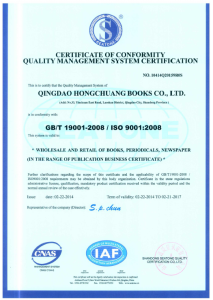
 ISO9001认证:
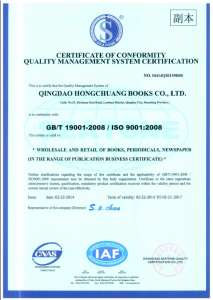
ISO9001认证:


 特别推荐:
特别推荐: